Understanding Zero Trust: A Key Component in Cybersecurity Audits
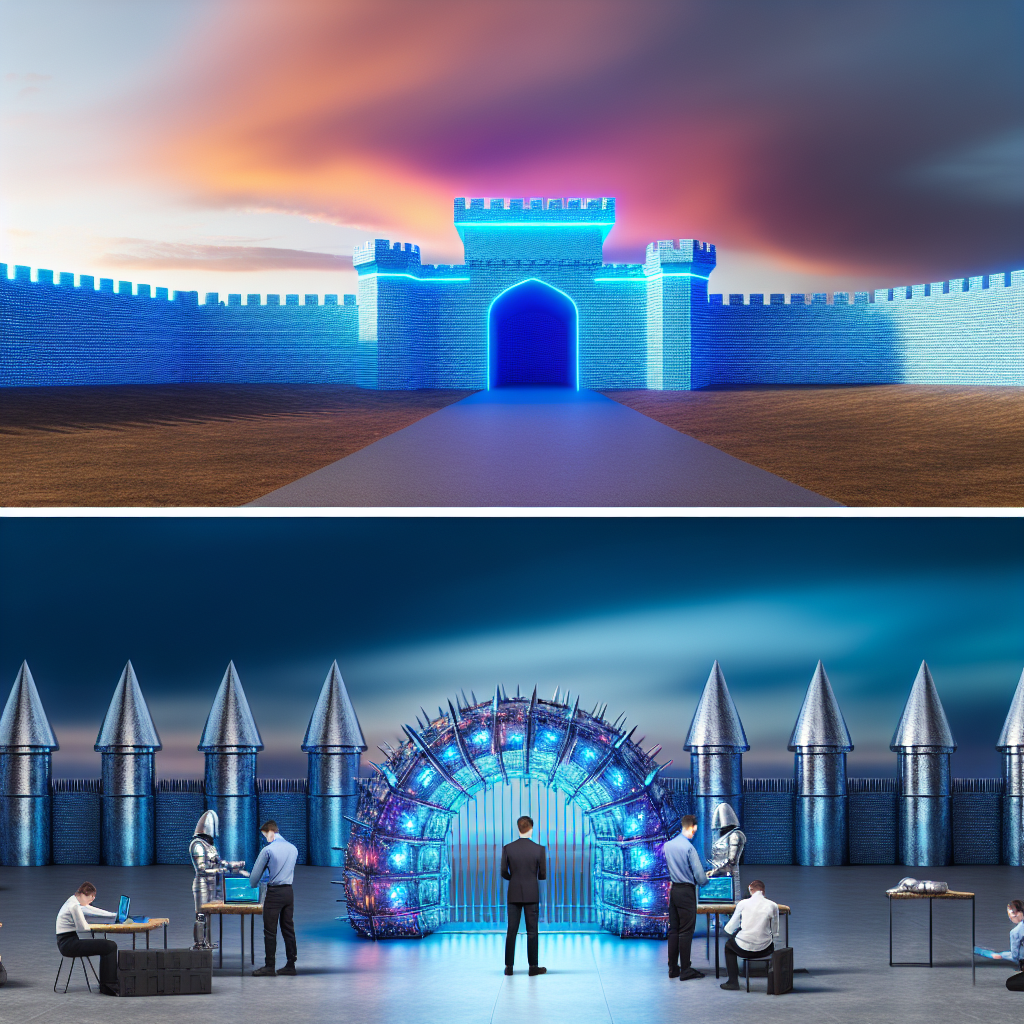
In the rapidly evolving landscape of digital threats, the concept of Zero Trust has emerged as a pivotal component in cybersecurity audits. As organizations increasingly rely on digital infrastructures, the traditional perimeter-based security models have become insufficient. This shift necessitates a more robust approach, where Zero Trust plays a crucial role. At its core, Zero Trust operates on the principle of “never trust, always verify,” which fundamentally changes how access to resources is managed and monitored.
The Zero Trust model assumes that threats could be both external and internal, thus requiring verification for every access request, regardless of its origin. This approach is particularly relevant in the context of cybersecurity audits, where the primary goal is to assess and enhance an organization’s security posture. By integrating Zero Trust principles, auditors can provide a more comprehensive evaluation of potential vulnerabilities and recommend strategies to mitigate risks effectively.
One of the key aspects of Zero Trust is the implementation of strict identity verification processes. This involves ensuring that every user, device, and application is authenticated and authorized before being granted access to critical resources. In a cybersecurity audit, this translates to a thorough examination of an organization’s identity and access management (IAM) protocols. Auditors assess whether these protocols are robust enough to prevent unauthorized access and if they align with the Zero Trust framework.
Moreover, Zero Trust emphasizes the importance of micro-segmentation, which involves dividing the network into smaller, isolated segments. This strategy limits the lateral movement of threats within the network, thereby containing potential breaches. During a cybersecurity audit, the effectiveness of micro-segmentation is evaluated to ensure that it adequately protects sensitive data and systems. Auditors look for evidence of well-defined network segments and assess the controls in place to monitor and manage traffic between these segments.
Another critical component of Zero Trust is continuous monitoring and real-time analytics. This involves the use of advanced technologies to detect and respond to threats as they occur. In the context of a cybersecurity audit, auditors examine the organization’s ability to monitor network activity continuously and analyze data for signs of suspicious behavior. This includes evaluating the tools and technologies in place for threat detection and response, as well as the processes for incident management.
Transitioning to a Zero Trust architecture also requires a cultural shift within the organization. Employees must be educated about the importance of cybersecurity and their role in maintaining a secure environment. During an audit, the effectiveness of security awareness programs is assessed to ensure that employees are equipped with the knowledge and skills necessary to adhere to Zero Trust principles.
In conclusion, understanding Zero Trust is essential for conducting effective cybersecurity audits. By focusing on identity verification, micro-segmentation, continuous monitoring, and fostering a security-conscious culture, organizations can significantly enhance their security posture. As cyber threats continue to evolve, adopting a Zero Trust approach not only strengthens defenses but also provides a comprehensive framework for identifying and addressing vulnerabilities. Consequently, cybersecurity audits that incorporate Zero Trust principles are better positioned to offer valuable insights and recommendations, ultimately contributing to a more secure digital environment.
Best Practices for Firewall Setup in IT Compliance
In the realm of IT compliance, the setup and maintenance of firewalls play a pivotal role in safeguarding sensitive data and ensuring the integrity of information systems. As organizations increasingly rely on digital infrastructures, the importance of robust firewall configurations cannot be overstated. Firewalls serve as the first line of defense against unauthorized access, malicious attacks, and data breaches. Therefore, understanding best practices for firewall setup is essential for maintaining compliance with cybersecurity standards and regulations.
To begin with, it is crucial to conduct a comprehensive risk assessment before implementing any firewall solution. This assessment should identify potential threats and vulnerabilities specific to the organization’s network environment. By understanding these risks, IT professionals can tailor firewall configurations to address the unique security needs of their organization. Moreover, this proactive approach aids in aligning firewall policies with broader organizational security objectives, thereby enhancing overall compliance efforts.
Once the risk assessment is complete, the next step involves selecting the appropriate type of firewall. There are several types of firewalls, including packet-filtering, stateful inspection, proxy, and next-generation firewalls. Each type offers distinct features and capabilities, and the choice should be based on the specific requirements of the organization. For instance, next-generation firewalls provide advanced threat detection and prevention capabilities, making them suitable for organizations with complex security needs.
After selecting the appropriate firewall, it is essential to establish a clear and concise firewall policy. This policy should define the rules and criteria for allowing or denying network traffic. It is advisable to adopt a default-deny approach, where all traffic is blocked by default unless explicitly permitted. This approach minimizes the risk of unauthorized access and ensures that only legitimate traffic is allowed through the network. Additionally, firewall policies should be regularly reviewed and updated to reflect changes in the network environment and emerging threats.
Furthermore, proper configuration of firewall rules is critical to ensuring effective protection. IT professionals should avoid overly permissive rules that could inadvertently expose the network to potential threats. Instead, rules should be specific and granular, allowing only the necessary traffic to pass through. It is also important to implement logging and monitoring mechanisms to track firewall activity and detect any suspicious behavior. Regular audits of firewall logs can help identify potential security incidents and facilitate timely responses.
In addition to technical configurations, organizations should prioritize employee training and awareness. Human error remains a significant factor in cybersecurity incidents, and educating employees about the importance of firewall security can mitigate this risk. Training programs should cover topics such as recognizing phishing attempts, understanding the implications of firewall policies, and reporting suspicious activities.
Finally, it is essential to stay informed about the latest developments in cybersecurity and firewall technologies. The threat landscape is constantly evolving, and new vulnerabilities and attack vectors emerge regularly. By keeping abreast of these changes, organizations can adapt their firewall strategies to address new challenges and maintain compliance with industry standards.
In conclusion, the setup and maintenance of firewalls are integral components of IT compliance and cybersecurity. By conducting thorough risk assessments, selecting appropriate firewall types, establishing clear policies, configuring rules meticulously, and fostering employee awareness, organizations can enhance their security posture and protect their digital assets effectively. As the digital landscape continues to evolve, adhering to these best practices will be crucial in safeguarding against emerging threats and ensuring compliance with cybersecurity regulations.
Enhancing Threat Detection Through Comprehensive Cybersecurity Audits
In today’s digital age, the importance of robust cybersecurity measures cannot be overstated. As organizations increasingly rely on digital infrastructure, the risk of cyber threats has grown exponentially. Consequently, enhancing threat detection has become a critical priority for businesses worldwide. One effective strategy to bolster an organization’s cybersecurity posture is through comprehensive cybersecurity audits. These audits serve as a vital tool in identifying vulnerabilities, assessing the effectiveness of existing security measures, and ultimately enhancing threat detection capabilities.
A cybersecurity audit is a systematic evaluation of an organization’s information systems, policies, and procedures. It aims to ensure that adequate security controls are in place to protect sensitive data and maintain the integrity of the network. By conducting regular audits, organizations can gain valuable insights into their security posture and identify areas that require improvement. This proactive approach not only helps in mitigating potential risks but also strengthens the organization’s ability to detect and respond to threats in a timely manner.
One of the primary benefits of a cybersecurity audit is its ability to uncover hidden vulnerabilities within an organization’s network. These vulnerabilities, if left unaddressed, can serve as entry points for cybercriminals. By identifying these weaknesses, organizations can take corrective actions to fortify their defenses. Moreover, audits provide a comprehensive overview of the organization’s security architecture, enabling the identification of outdated or ineffective security measures. This, in turn, allows for the implementation of more robust and up-to-date solutions, thereby enhancing the overall threat detection capabilities.
In addition to identifying vulnerabilities, cybersecurity audits also play a crucial role in assessing the effectiveness of an organization’s incident response plan. A well-structured incident response plan is essential for minimizing the impact of a cyber attack. Through audits, organizations can evaluate the efficiency of their response strategies and make necessary adjustments to ensure a swift and effective reaction to potential threats. This continuous improvement process is vital for maintaining a resilient security posture in the face of evolving cyber threats.
Furthermore, cybersecurity audits facilitate compliance with industry standards and regulations. Many sectors, such as finance and healthcare, are subject to stringent regulatory requirements regarding data protection and privacy. Regular audits help organizations ensure that they are in compliance with these regulations, thereby avoiding potential legal and financial repercussions. Compliance not only protects the organization but also enhances its reputation and builds trust with clients and stakeholders.
Another significant advantage of conducting cybersecurity audits is the opportunity for employee education and awareness. During the audit process, employees can gain a better understanding of the organization’s security policies and procedures. This increased awareness fosters a culture of security within the organization, encouraging employees to adopt best practices and remain vigilant against potential threats. A well-informed workforce is a critical component of an effective cybersecurity strategy, as human error is often a significant factor in security breaches.
In conclusion, comprehensive cybersecurity audits are an indispensable tool for enhancing threat detection and strengthening an organization’s overall security posture. By identifying vulnerabilities, assessing incident response plans, ensuring regulatory compliance, and promoting employee awareness, these audits provide a holistic approach to cybersecurity. As cyber threats continue to evolve, organizations must prioritize regular audits to stay ahead of potential risks and safeguard their digital assets. Through this proactive approach, businesses can not only protect themselves from cyber threats but also build a resilient and secure digital environment for the future.
Network Intrusion Prevention: Insights from Cybersecurity Audits
In the ever-evolving landscape of digital threats, network intrusion prevention has become a cornerstone of cybersecurity strategies. As organizations increasingly rely on digital infrastructures, the need to safeguard these systems from unauthorized access and malicious activities has never been more critical. Cybersecurity audits play a pivotal role in this context, offering valuable insights into the effectiveness of existing security measures and identifying areas for improvement. Through these audits, organizations can better understand the vulnerabilities within their networks and implement robust intrusion prevention systems to mitigate potential risks.
One of the primary insights gained from cybersecurity audits is the identification of common vulnerabilities that could be exploited by cybercriminals. These audits often reveal outdated software, misconfigured systems, and inadequate access controls, all of which can serve as entry points for intruders. By addressing these vulnerabilities, organizations can significantly reduce the likelihood of a successful intrusion. Moreover, audits provide a comprehensive overview of the network architecture, enabling security teams to pinpoint weaknesses and fortify defenses accordingly.
In addition to identifying vulnerabilities, cybersecurity audits also assess the effectiveness of existing intrusion prevention systems (IPS). These systems are designed to detect and block suspicious activities in real-time, thereby preventing unauthorized access to the network. However, the efficacy of an IPS largely depends on its configuration and the quality of threat intelligence it receives. Audits help ensure that these systems are properly configured and updated with the latest threat data, thereby enhancing their ability to thwart potential attacks.
Furthermore, cybersecurity audits emphasize the importance of continuous monitoring and incident response. While intrusion prevention systems are crucial, they are not infallible. Cyber threats are constantly evolving, and attackers are becoming increasingly sophisticated in their methods. As such, organizations must adopt a proactive approach to network security, which includes continuous monitoring for unusual activities and a well-defined incident response plan. Audits can evaluate the effectiveness of these measures, ensuring that organizations are prepared to respond swiftly and effectively in the event of a breach.
Another critical insight from cybersecurity audits is the role of employee awareness and training in network intrusion prevention. Human error remains one of the leading causes of security breaches, often due to a lack of awareness or understanding of security protocols. Audits can highlight gaps in employee training programs and recommend strategies to enhance security awareness across the organization. By fostering a culture of security consciousness, organizations can empower their employees to act as the first line of defense against potential intrusions.
Moreover, audits underscore the importance of a layered security approach. Relying solely on a single security measure, such as an IPS, is insufficient in today’s complex threat environment. Instead, organizations should implement a multi-layered defense strategy that includes firewalls, encryption, access controls, and regular security assessments. This comprehensive approach ensures that even if one layer is compromised, others remain in place to protect the network.
In conclusion, cybersecurity audits provide invaluable insights into network intrusion prevention, highlighting vulnerabilities, assessing the effectiveness of existing measures, and emphasizing the need for continuous monitoring and employee training. By leveraging these insights, organizations can enhance their security posture and better protect their digital assets from the ever-present threat of cyber intrusions. As the digital landscape continues to evolve, the role of cybersecurity audits in safeguarding networks will remain indispensable, guiding organizations toward more resilient and secure infrastructures.
Endpoint Protection Strategies in the Context of Cybersecurity Audits
In the ever-evolving landscape of cybersecurity, endpoint protection has emerged as a critical component of comprehensive security strategies. As organizations increasingly rely on a multitude of devices to conduct business, the need for robust endpoint protection becomes paramount. This necessity is further underscored during cybersecurity audits, where endpoint security is scrutinized to ensure that vulnerabilities are minimized and data integrity is maintained. Understanding the role of endpoint protection within the context of cybersecurity audits is essential for organizations aiming to safeguard their digital assets effectively.
Endpoint protection refers to the security measures implemented to protect devices such as laptops, desktops, and mobile devices from cyber threats. These endpoints are often the most vulnerable entry points for cyberattacks, making them a focal point during cybersecurity audits. Auditors assess the effectiveness of endpoint protection strategies by examining the deployment of antivirus software, firewalls, and intrusion detection systems. They also evaluate the implementation of security patches and updates, which are crucial for defending against newly discovered vulnerabilities. By ensuring that these measures are in place and functioning correctly, organizations can significantly reduce the risk of unauthorized access and data breaches.
Moreover, cybersecurity audits delve into the policies and procedures governing endpoint protection. This includes assessing the organization’s approach to device management, such as the enforcement of strong password policies and the use of encryption to protect sensitive data. Auditors also examine the organization’s incident response plan, which outlines the steps to be taken in the event of a security breach. A well-defined incident response plan is vital for minimizing the impact of a cyberattack and ensuring a swift recovery. By evaluating these aspects, auditors can provide valuable insights into the organization’s overall security posture and recommend improvements where necessary.
In addition to technical measures, cybersecurity audits also consider the human element of endpoint protection. Employees play a crucial role in maintaining the security of endpoints, and their actions can either strengthen or weaken an organization’s defenses. Therefore, auditors assess the effectiveness of security awareness training programs, which are designed to educate employees about the latest cyber threats and best practices for safeguarding their devices. By fostering a culture of security awareness, organizations can empower their employees to become the first line of defense against cyber threats.
Furthermore, the integration of advanced technologies such as artificial intelligence and machine learning into endpoint protection strategies is becoming increasingly prevalent. These technologies enable organizations to detect and respond to threats in real-time, enhancing their ability to protect endpoints from sophisticated attacks. During cybersecurity audits, the implementation and effectiveness of these technologies are evaluated to ensure that they are contributing positively to the organization’s security framework. By leveraging these advanced tools, organizations can stay ahead of emerging threats and maintain a robust security posture.
In conclusion, endpoint protection is a vital aspect of cybersecurity audits, as it directly impacts an organization’s ability to defend against cyber threats. By examining the technical measures, policies, and human factors involved in endpoint protection, auditors can provide comprehensive insights into an organization’s security practices. As cyber threats continue to evolve, organizations must remain vigilant and proactive in their approach to endpoint protection, ensuring that their strategies are continuously updated and aligned with the latest industry standards. Through diligent audits and the implementation of effective endpoint protection strategies, organizations can safeguard their digital assets and maintain the trust of their stakeholders.
Enhance your organization’s security posture with our comprehensive Cybersecurity Insights: Cybersecurity Audit. Discover vulnerabilities, ensure compliance, and protect your data. Learn more and schedule your audit today!